On January 20, 2026, Cloudflare announced a significant security update addressing a vulnerability in its Automatic Certificate Management Environment (ACME) validation logic. This flaw had the potential to allow attackers to bypass Web Application Firewalls (WAF), posing a serious threat to the integrity of web applications and the safety of user data. In this article, we will delve into the details of the ACME validation bug, its implications, and the best practices for securing web applications against similar threats.
Understanding ACME and Its Importance
The Automatic Certificate Management Environment (ACME) protocol is a critical component in the process of obtaining and renewing SSL/TLS certificates. It automates the interaction between certificate authorities and web servers, ensuring that websites can establish secure connections with their users. By simplifying the certificate management process, ACME plays a vital role in enhancing web security.
The Vulnerability Explained
The vulnerability identified in Cloudflare's ACME validation logic allowed for a potential bypass of the Web Application Firewall (WAF). This flaw could enable malicious actors to exploit the certificate issuance process, potentially leading to unauthorized access to sensitive data or the ability to impersonate legitimate websites. Research indicates that vulnerabilities like this can have far-reaching consequences for organizations, including data breaches and loss of user trust.
How the Bypass Worked
While the specific technical details of the vulnerability have not been fully disclosed, it is understood that the flaw resided in the way ACME handled validation requests. Attackers could craft specific requests that would trick the validation process, allowing them to bypass the WAF protections that are typically in place to safeguard web applications. This method of attack underscores the need for robust security measures in automated systems.
Implications of the ACME Validation Bug
The implications of this vulnerability are significant. By allowing a WAF bypass, attackers could potentially gain access to sensitive information, execute malicious scripts, or redirect users to phishing sites. This not only jeopardizes the security of individual websites but also undermines user trust in the broader internet ecosystem. Industry experts note that such vulnerabilities can lead to severe repercussions for affected organizations, including financial losses and reputational damage.
Potential Risks for Organizations
- Data Breaches: Unauthorized access to sensitive data can lead to severe financial and reputational damage.
- Service Disruption: Exploiting this vulnerability could result in service outages, affecting business operations.
- Legal Consequences: Organizations may face legal repercussions if they fail to protect user data adequately.
Cloudflare's Response to the ACME Validation Bug
In response to the discovery of this vulnerability, Cloudflare acted swiftly to implement a fix. The company released a security update that addressed the ACME validation logic flaw, ensuring that the WAF protections are now more robust against potential bypass attempts. This proactive approach demonstrates Cloudflare's commitment to maintaining security standards.
Steps Taken by Cloudflare
- Patch Deployment: Cloudflare deployed a patch to its systems to close the vulnerability.
- Monitoring: The company has increased monitoring of its systems to detect any unusual activity that may indicate attempts to exploit the vulnerability.
- User Notification: Cloudflare has informed its users about the vulnerability and the steps taken to mitigate it.
Best Practices for Organizations
While Cloudflare has addressed this specific vulnerability, organizations must remain vigilant and adopt best practices to enhance their overall cybersecurity posture. Here are some recommended strategies:
1. Regularly Update Security Protocols
Organizations should ensure that their security protocols, including WAF configurations and SSL/TLS certificates, are regularly updated to protect against emerging threats. This includes keeping software up to date and applying security patches promptly.
2. Conduct Vulnerability Assessments
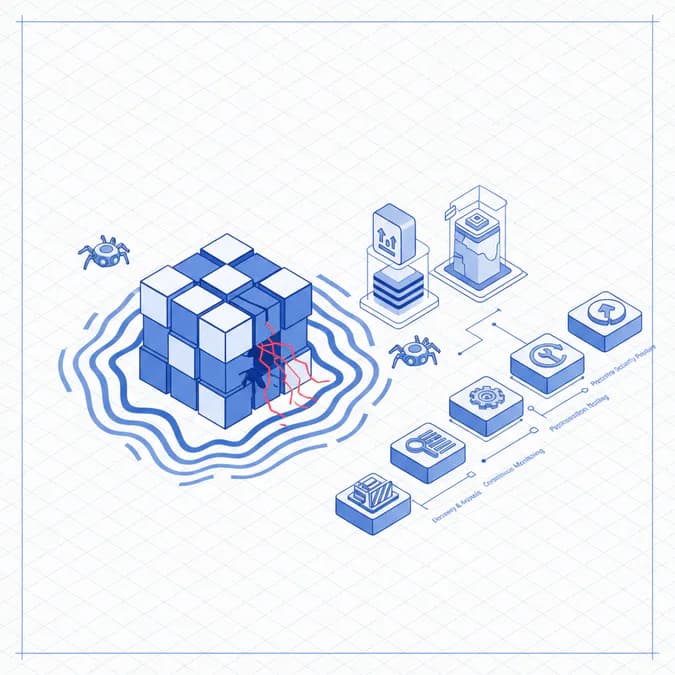
Regular vulnerability assessments can help identify potential weaknesses in your systems before they can be exploited by attackers. This proactive approach is essential for maintaining robust security and should be part of an organization's routine security practices.
3. Implement Multi-Factor Authentication
Using multi-factor authentication (MFA) can add an additional layer of security, making it more difficult for unauthorized users to gain access to sensitive systems. MFA is a critical component of a comprehensive security strategy.
4. Educate Employees
Training employees on cybersecurity best practices can help reduce the risk of human error, which is often a significant factor in security breaches. Regular training sessions can keep security awareness high and empower employees to recognize potential threats.
5. Monitor for Anomalies
Implementing continuous monitoring solutions can help detect unusual activity that may indicate an attempted breach. This can include automated alerts for suspicious behavior, allowing organizations to respond quickly to potential threats.
The Bottom Line
The recent vulnerability in Cloudflare's ACME validation logic highlights the importance of robust security measures in today's digital landscape. As organizations increasingly rely on automated systems for certificate management, understanding and mitigating potential vulnerabilities becomes crucial. By staying informed and adopting best practices, organizations can better protect themselves against the evolving threat landscape.
In conclusion, while Cloudflare has taken decisive action to fix this vulnerability, the responsibility for cybersecurity lies with all organizations. By prioritizing security and remaining vigilant, businesses can safeguard their operations and maintain the trust of their users.
Key Takeaways
- The ACME validation bug posed significant security risks by allowing WAF bypass.
- Cloudflare has implemented a fix to enhance security measures.
- Organizations should adopt best practices to protect against similar vulnerabilities.
Frequently Asked Questions (FAQ)
What is the ACME validation bug?
The ACME validation bug refers to a vulnerability in Cloudflare's ACME validation logic that allowed attackers to bypass Web Application Firewalls.
How can organizations protect against similar vulnerabilities?
Organizations can protect against similar vulnerabilities by regularly updating security protocols, conducting vulnerability assessments, and implementing multi-factor authentication.
What steps did Cloudflare take to address the ACME validation bug?
Cloudflare deployed a patch, increased monitoring, and notified users about the vulnerability and the measures taken to mitigate it.
For further reading, organizations may refer to resources from CISA and NIST for best practices in cybersecurity.