Table of Contents
- Key Takeaways
- Introduction to Vulnerability Management
- Understanding the AutoSecT VMDR Tool
- Key Features and Benefits
- Cybersecurity Challenges Addressed
- Implementation Strategies
- FAQ Section
- Conclusion
- Sources
Key Takeaways

The AutoSecT VMDR tool revolutionizes vuln

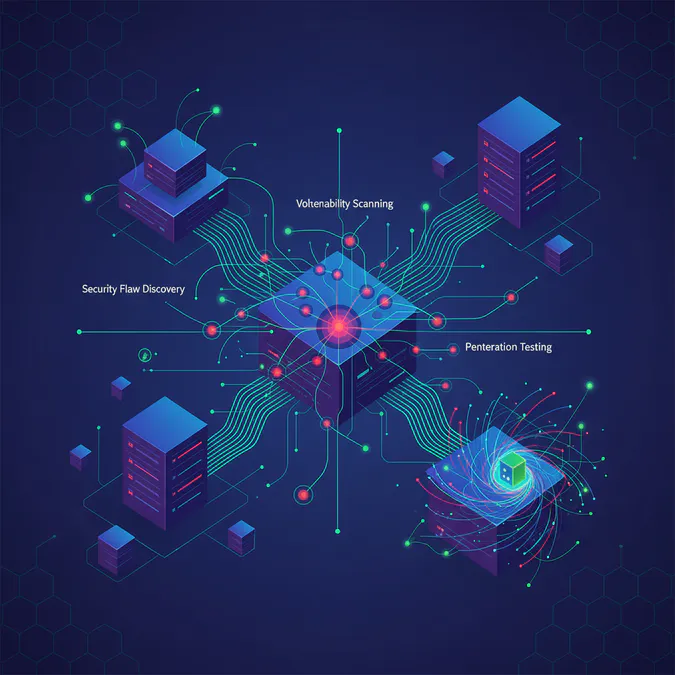
Introduction to Vulnerability Management
Vulnerability management is a proactive approach to identifying, evaluating, treating, and reporting security vulnerabilities in systems and software. This process is vital for organizations to protect sensitive data and maintain compliance with industry regulations. With cyber threats becoming increasingly sophisticated, organizations must adopt robust vulnerability management strategies to safeguard their assets. Research indicates that cybercrime is projected to cost the world $10.5 trillion annually by 2025, highlighting the urgent need for effective vulnerability management.

Understanding the AutoSecT VMDR Tool
The AutoSecT VMDR (Vulnerability Management, Detection, and Response) tool is engineered to streamline the vulnerability management process. By focusing on the critical aspects of vulnerability management, AutoSecT aims to provide organizations with a clear understanding of their security posture. The tool integrates various functionalities, allowing users to manage vulnerabilities effectively and respond to threats in real-time. As noted by a cybersecurity analyst, "The AutoSecT VMDR tool is essential for organizations looking to enhance their security posture and respond to vulnerabilities swiftly."
Key Features and Benefits
The AutoSecT VMDR tool boasts several features that enhance its usability and effectiveness:
- Centralized Dashboard: Offers a comprehensive view of vulnerabilities across the organization, enabling quick assessment and prioritization.
- Automated Scanning: Regularly scans systems for vulnerabilities, ensuring that organizations stay ahead of potential threats. Research indicates that organizations using automated tools experience a 50% reduction in vulnerability response times.
- Real-time Alerts: Provides immediate notifications of newly discovered vulnerabilities, allowing for prompt action.
- Integration Capabilities: Seamlessly integrates with existing security tools and frameworks, enhancing overall security operations.
These features not only simplify the management of vulnerabilities but also empower organizations to respond swiftly to emerging threats, thereby reducing the risk of data breaches.
Cybersecurity Challenges Addressed
Organizations today face several cybersecurity challenges, including:
- Increased Attack Surface: With the rise of remote work and cloud services, the number of potential entry points for attackers has dramatically increased.
- Complexity of IT Environments: Many organizations operate in hybrid environments, making it difficult to maintain visibility and control over vulnerabilities.
- Resource Constraints: Limited budgets and personnel can hinder effective vulnerability management efforts.
The AutoSecT VMDR tool addresses these challenges by providing a user-friendly interface and automated processes that reduce the burden on IT teams, allowing them to focus on strategic initiatives rather than manual vulnerability assessments.
Implementation Strategies
To effectively implement the AutoSecT VMDR tool, organizations should consider the following strategies:
- Assess Current Security Posture: Understand existing vulnerabilities and security measures in place.
- Define Clear Objectives: Establish what the organization aims to achieve with the VMDR tool, such as reducing response times or improving compliance.
- Train Staff: Ensure that team members are adequately trained on how to use the tool and interpret its findings.
- Regularly Review and Update: Continuously monitor the effectiveness of the tool and make necessary adjustments based on evolving threats and organizational needs.
By following these steps, organizations can maximize the benefits of the AutoSecT VMDR tool and enhance their overall cybersecurity strategy.
FAQ Section
Q1: What is vulnerability management?
A1: Vulnerability management is the process of identifying, evaluating, treating, and reporting security vulnerabilities in systems and software to protect sensitive data and maintain compliance.
Q2: How does the AutoSecT VMDR tool help in vulnerability management?
A2: The AutoSecT VMDR tool streamlines the vulnerability management process by providing automated scanning, real-time alerts, and integration capabilities with existing security tools.
Q3: What are the benefits of using the AutoSecT VMDR tool?
A3: Benefits include a centralized dashboard for quick assessment, automated vulnerability scanning, real-time alerts for immediate action, and seamless integration with other security frameworks.
Conclusion
The AutoSecT VMDR tool representa significant advancement in vulnerability management, addressing the pressing cybersecurity challenges faced by organizations today. By simplifying the process and providing essential features, it empowers organizations to take control of their security posture and respond effectively to vulnerabilities. For more information about the AutoSecT VMDR tool, visit Security Boulevard.




