Software-as-a-Service (SaaS) has evolved from a convenient IT option to the fundamental infrastructure powering modern business operations. Platforms like Salesforce, Workday, Microsoft 365, and Slack have become indispensable tools that organizations rely on daily. However, this widespread adoption has created an unexpected consequence: SaaS security supply chains have emerged as one of cybersecurity's most vulnerable attack surfaces.
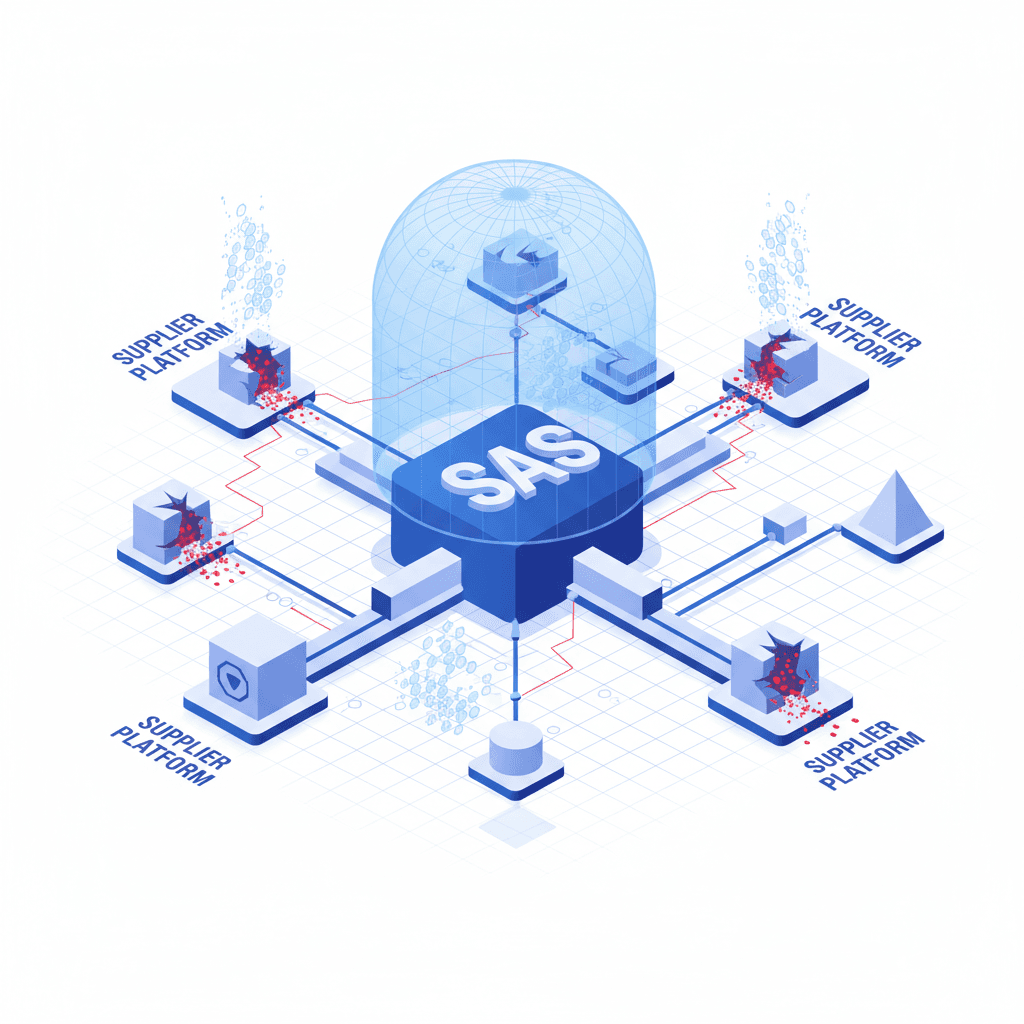
The SaaS ecosystem operates on a complex web of interconnected services, third-party integrations, and API connections. Each connection point represents a potential entry vector for cybercriminals. When a single SaaS provider experiences a security breach, the impact can cascade across hundreds or thousands of organizations simultaneously.
Understanding the SaaS Security Supply Chain Risk
The traditional concept of supply chain security focused primarily on physical goods and manufacturing processes. In the digital realm, SaaS security concerns center on the intricate relationships between primary service providers, their subcontractors, integration partners, and the countless APIs that enable data flow between systems.
Modern businesses typically use 80 to 100 different SaaS applications, many of which share data and permissions. This creates a sprawling attack surface that's difficult to monitor and secure. When one application in this chain is compromised, attackers can potentially pivot to access other connected systems, multiplying the damage exponentially.
Why SaaS Platforms Are Attractive Targets
Cybercriminals have recognized that targeting SaaS providers offers significant advantages over attacking individual organizations. A successful breach of a major SaaS platform can provide access to thousands of customer environments simultaneously. These platforms store vast amounts of sensitive business data, intellectual property, and customer information, making them high-value targets.
Furthermore, many organizations place implicit trust in their SaaS providers, sometimes overlooking security configurations or failing to implement proper access controls. This trust, while often necessary for business operations, can create blind spots in security posture.
Common Vulnerabilities in SaaS Supply Chains
Several key vulnerabilities plague SaaS supply chains. Misconfigured permissions and overly broad access rights frequently allow unauthorized data exposure. Third-party integrations often receive excessive privileges without proper vetting or ongoing monitoring. API security weaknesses can enable data exfiltration or unauthorized access.
Insufficient visibility into the full scope of SaaS usage within an organization—often called shadow IT—compounds these problems. Employees may adopt SaaS tools without IT department approval, creating unmanaged security gaps.
Protecting Your Organization
Addressing SaaS security requires a multi-layered approach. Organizations should implement comprehensive SaaS security posture management (SSPM) solutions that continuously monitor configurations, permissions, and compliance across all SaaS applications.
Regular security assessments of SaaS providers and their subcontractors are essential. Organizations should demand transparency about security practices, incident response procedures, and data handling policies. Implementing zero-trust architecture principles, where no user or application is automatically trusted, helps minimize potential damage from compromised accounts.
Strict access controls based on the principle of least privilege ensure users and integrations only have the permissions absolutely necessary for their functions. Multi-factor authentication should be mandatory across all SaaS platforms.
The Path Forward
As SaaS continues to dominate the business technology landscape, security teams must evolve their strategies to address supply chain risks. This means moving beyond perimeter-based security models to embrace continuous monitoring, automated threat detection, and proactive risk management.
Organizations that recognize SaaS supply chains as critical infrastructure deserving dedicated security resources will be better positioned to prevent breaches and maintain business continuity. The question is no longer whether to use SaaS, but how to use it securely in an increasingly interconnected digital ecosystem.